Unlimited access to Ultra Librarian symbols, footprints and 3D STEP models is now available from Digi-Key. The distributor has worked with EDA value added reseller, EMA Design Automation, to remove the download limits of Ultra Librarian EDA and CAD models. “We now have model coverage for over 1.25 million parts,” said Randall Restle, vice president, applications engineering at Digi-Key. “Our ...
Software
The latest Electronics Weekly product news involving software, such as Linux, MathWorks and PCB designers.
Comment: Many happy returns to open source
The birth of open source 20 years ago considerably accelerated the development of both software and hardware. Which software initiative is supported by Facebook and Google; promoted by Microsoft and IBM? Twenty years ago the phrase “open source” was first used and the development of software – and hardware – was changed forever. Very few designers today will not use ...
Neural network SDK for PowerVR GPUs
Imagination Technologies has announced a software design kit (SDK) for developing neural networks on its PowerVR graphics processors (GPUs). It is aimed at convolutional neural networks, and both an API and SDK are included, as well as an image for flashing on to an Acer Chromebook R13 for hardware development. Future versions of the API and SDK library will allow ...
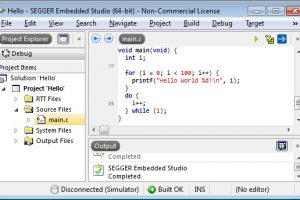
Free Segger Embedded Studio for Nordic nRF51 and nRF52
Nordic Semiconductor has licensed Embedded Studio from Segger Microcontroller on behalf of Nordic customers – in particular those developing applications for its nRF51 and nRF52 Bluetooth chips – both of which have spare user-accessible processing power. Embedded Studio is an integrated development environment (IDE) for managing, building, testing, and deploying embedded applications, which includes: a project manager, source code editor, C/C++ ...
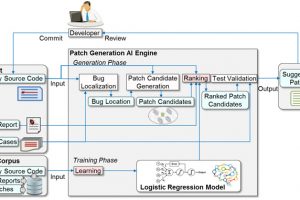
Software bugs fixed automatically with AI and Big Data
Fujitsu Laboratories creates artificial intelligence that automatically creates patches for software bugs
Researchers reveal so-called ‘KRACK’ vulnerability in WPA2 Wi-Fi protocol
UPDATED - WPA2, the security commonly used on Wi-Fi communication, has a built-in vulnerability, according to researchers from the University of Leuven - while experts have urged a sense of perspective over the so-called 'KRACK' attacks.
Cobham validates core networks as they go virtual
Cobham Wireless has launched TeraVM LaaS (lab-as-a-service) for core network testing, intending to support mobile operator networks as they shift towards ‘network function virtualisation’ (NFV) infrastructure. “The introduction of LTE-Advanced and 5G requires mobile operators to invest in virtual core network technology, in order to operate with dynamic flexibility and reduced cost,” said the firm. “TeraVM LaaS provides a comprehensive ...
Imperas joins RISC-V Foundation
Imperas Software has become a member of the RISC-V Foundation, at the same time as it made virtual platform and model support available for the RISC-V architecture. RISC-V Foundation drives the adoption of the RISC-V instruction set architecture (ISA) – a RISC architecture originally developed at the University of California, Berkeley, now touted as an open-source competitor to the ARM ...
Software algorithms secure embedded designs
Segger has introduced a library of cryptographic algorithms written entirely in C. Called emCrypt, it includes block ciphers, hashes, MACs, and digital signatures required to meet the demanding cryptographic needs of embedded devices. Having been designed from the ground up for use in memory-constrained embedded systems, emCrypt uses minimal resources in respect of memory footprint (RAM/ROM) as well as CPU ...
Georgia Tech finds subtle Linux vunerability
Uninitialised variables are a critical attack vector that can be reliably exploited by hackers to launch privilege escalation attacks in the Linux kernel, according to research at the Georgia Institute of Technology. “While other kernel bugs and vulnerabilities have been examined and remedied, uninitialised-use bugs are not well studied, and to date, no practical defence mechanisms have been developed to ...
 Electronics Weekly
Electronics Weekly